Tingkatkanlah skillmu sekarang juga.
Yuk persiapkan suksesmu, dimulai dari mempelajari teknologi saat ini.

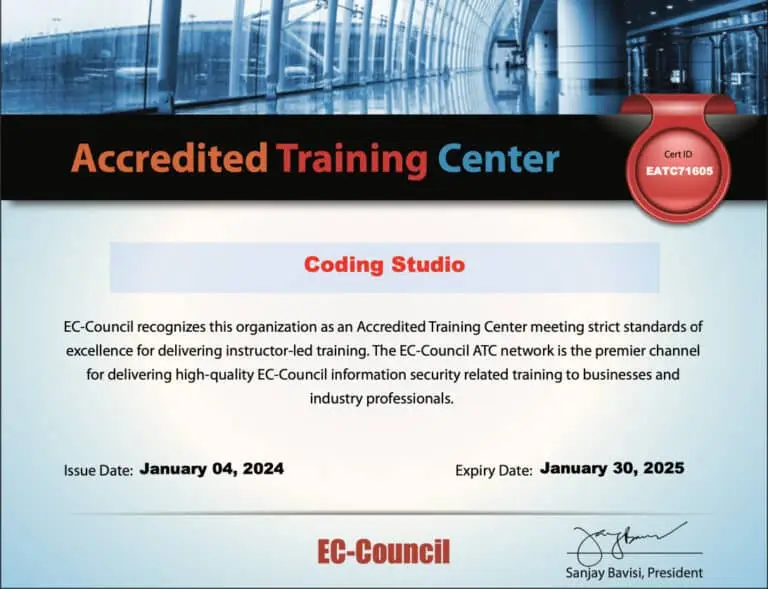
Coding Studio Verified Program - Sertifikasi CEH
Raih Sertifikasi Internasional untuk kamu yang ingin dapat kerja dan tingkatkan karirmu dengan sertifikasi yang telah diakui lembaga internasional terpercaya.


Sertifikasi CEH (Certified Ethical Hacker) dari EC-Council adalah sertifikasi yang dirancang untuk mengukur keterampilan seorang profesional dalam mengidentifikasi kelemahan keamanan dalam sistem komputer dan jaringan dengan metode yang digunakan oleh penyerang yang bersifat etis.
EC-Council (International Council of E-Commerce Consultants) adalah organisasi yang memberikan sertifikasi keamanan informasi dan melatih profesional keamanan.
Sertifikasi CEH ini terpakai untuk melamar kerja di bidang cyber security di perusahaan.
Permintaan pekerjaan di bidang cyber security sangat banyak.
Menjadi seorang cyber security dengan sertifikasi ceh akan memiliki peluang bayaran yang tinggi dengan rata-rata gaji di 8-15 juta
Cyber security akan selalu dibutuhkan selama masih ada digital. Jadi buat yang berkarir di industri ini akan punya masa depan yang cerah
72% lowongan pekerjaan membutuhkan sertifikasi IT/Komputer (CPNS/BUMN/Swasta).
Alasan mengapa sertifikasi profesional sangat bermanfaat bagi siapa pun dalam karier mereka adalah karena sertifikasi tersebut secara otomatis meningkatkan peluang untuk mendapatkan pekerjaan dan untuk memenuhi persyaratan melamar pekerjaan dimanapun perusahaan atau instititusi yang ingin anda lamar.
Survei terbaru yang diterbitkan oleh Wired Workplace menemukan bahwa 56% profesional TI yang menyelesaikan sertifikasi mendapat kenaikan gaji atau bonus dan 29% menerima promosi.
Studi lain yang dilakukan oleh DICE (pusat karir online) menemukan bahwa para profesional tidak hanya merasa lebih mudah mendapatkan pekerjaan setelah mereka mendapatkan sertifikasi, namun mereka juga sering ditawari gaji yang lebih tinggi (sebanyak 16% lebih tinggi).
Mereka yang mendapat jabatan terbaik adalah orang-orang yang terus belajar dan berlatih secara terus-menerus.
Salah satu keuntungan besar lainnya dari sertifikasi profesional adalah sertifikasi tersebut akan selalu memungkinkan Anda untuk terus berkembang. Tentunya sertifikasi membantu perusahaan melihat skill anda tervalidasi oleh lembaga resmi.


Maestro (Pengajar) yang melatih Kamu adalah seorang praktisi di industrinya dengan pengalaman minimal 2 tahun.

Kurikulum didesain sesuai standar industri dan akan up to date mengikuti perkembangan zaman.

Kamu tidak hanya belajar dalam sesi training saja, tapi juga mendapatkan sesi mentoring untuk membantu sharing real experience.

Pendekatan pembelajaran yang berpusat pada project yang menantang, berarti, dan berorientasi pada masalah.

Tidak hanya belajar hard skill tapi Kamu juga akan belajar soft skill yang akan sangat menunjang karir Kamu.

Kamu akan terkoneksi dengan komunitas kami dan Kamu pun yang telah lulus dapat berkontribusi dalam komunitas.
Langkah-langkah yang harus diambil untuk memperoleh sertifikasi Internasional
Persiapkan dirimu dengan matang untuk meraih sertifikasi internasional dan buka pintu karier digital yang cerah
Mengikuti ujian sertifikasi internasional secara offline ataupun online melalui Coding Studio selaku Authorized Test Center
Setelah lulus dari ujian, kamu akan mendapatkan sertifikat yang diakui internasional dan dapat divalidasi keasliannya
Learn how to use the latest techniques and tools to perform footprinting and reconnaissance, a critical pre-attack phase of the ethical hacking process.
Learn about the various system hacking methodologies used to discover system and network vulnerabilities, including steganography, steganalysis attacks, and how to cover tracks.
Learn about different types of malware (Trojan, viruses, worms, etc.), APT and fileless malware, malware analysis procedures, and malware countermeasures.
Learn about packet-sniffing techniques and their uses for discovering network vulnerabilities, plus countermeasures to defend against sniffing attacks.
Learn social engineering concepts and techniques, including how to identify theft attempts, audit human-level vulnerabilities, and suggest social engineering countermeasures.
Learn about different Denial of Service (DoS) and Distributed DoS (DDoS) attack techniques, plus the tools used to audit a target and devise DoS and DDoS countermeasures and protections.
Learn the various session hijacking techniques used to discover network-level session management, authentication, authorization, and cryptographic weaknesses and associated countermeasures.
Learn about firewall, intrusion detection system (IDS), and honeypot evasion techniques; the tools used to audit a network perimeter for weaknesses; and countermeasures.
Learn about web server attacks, including a comprehensive attack methodology used to audit vulnerabilities in web server infrastructures and countermeasures.
Learn about web application attacks, including a comprehensive web application hacking methodology used to audit vulnerabilities in web applications and countermeasures.
Learn about SQL injection attack techniques, evasion techniques, and SQL injection countermeasures.
Learn about different types of encryption, threats, hacking methodologies, hacking tools, security tools, and countermeasures for wireless networks.
Learn mobile platform attack vectors, Android and iOS hacking, mobile device management, mobile security guidelines, and security tools.
Learn different types of Internet of Things (IoT) and operational technology (OT) attacks, hacking methodologies, hacking tools, and countermeasures.
Learn different cloud computing concepts, such as container technologies and serverless computing, various cloud computing threats, attacks, hacking methodologies, and cloud security techniques and tools.
Learn about encryption algorithms, cryptography tools, Public Key Infrastructure (PKI), email encryption, disk encryption, cryptography attacks, and cryptanalysis tools.






*HARGA EARLY BIRD
Yuk persiapkan suksesmu, dimulai dari mempelajari teknologi saat ini.

